Java Google Http Client Application/x-www-form-urlencoded File Upload
The Google OAuth two.0 system supports server-to-server interactions such as those between a web application and a Google service. For this scenario you need a service account, which is an business relationship that belongs to your application instead of to an individual end user. Your application calls Google APIs on behalf of the service account, so users aren't direct involved. This scenario is sometimes called "two-legged OAuth," or "2LO." (The related term "iii-legged OAuth" refers to scenarios in which your application calls Google APIs on behalf of end users, and in which user consent is sometimes required.)
Typically, an application uses a service business relationship when the application uses Google APIs to piece of work with its own information rather than a user's information. For example, an application that uses Google Cloud Datastore for data persistence would employ a service account to cosign its calls to the Google Cloud Datastore API.
Google Workspace domain administrators can also grant service accounts domain-wide authority to access user data on behalf of users in the domain.
This document describes how an application can complete the server-to-server OAuth 2.0 menstruum past using either a Google APIs client library (recommended) or HTTP.
Overview
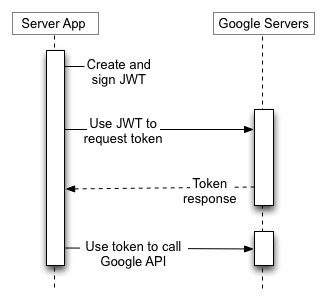
To support server-to-server interactions, first create a service account for your projection in the API Console. If y'all want to admission user data for users in your Google Workspace account, then delegate domain-wide access to the service account.
And so, your application prepares to brand authorized API calls by using the service account's credentials to request an admission token from the OAuth 2.0 auth server.
Finally, your application can use the access token to call Google APIs.
Creating a service account
A service account's credentials include a generated email address that is unique and at least ane public/private primal pair. If domain-wide delegation is enabled, then a client ID is also part of the service account's credentials.
If your application runs on Google App Engine, a service account is set automatically when yous create your project.
If your awarding runs on Google Compute Engine, a service account is also set up automatically when yous create your project, but you must specify the scopes that your application needs access to when you lot create a Google Compute Engine instance. For more data, run into Preparing an case to employ service accounts.
If your application doesn't run on Google App Engine or Google Compute Engine, y'all must obtain these credentials in the Google API Console. To generate service-account credentials, or to view the public credentials that you've already generated, exercise the following:
Showtime, create a service account:
- Open up the Service accounts page.
- If prompted, select a projection, or create a new i.
- Click Create service business relationship.
- Under Service account details, type a name, ID, and description for the service business relationship, then click Create and continue.
- Optional: Under Grant this service account access to project, select the IAM roles to grant to the service business relationship.
- Click Go along.
- Optional: Under Grant users access to this service account, add the users or groups that are immune to use and manage the service business relationship.
- Click Done.
- Click Create key, and so click Create.
Adjacent, create a service business relationship key:
- Click the e-mail address for the service account y'all created.
- Click the Keys tab.
- In the Add key drop-down list, select Create new fundamental.
- Click Create.
Your new public/private key pair is generated and downloaded to your machine; it serves every bit the only re-create of the individual key. You are responsible for storing it securely. If you lose this key pair, you will need to generate a new 1.
Yous tin return to the API Console at any time to view the email address, public key fingerprints, and other information, or to generate boosted public/private key pairs. For more than details about service account credentials in the API Console, see Service accounts in the API Panel assist file.
Have note of the service account's email address and store the service account's private key file in a location accessible to your awarding. Your application needs them to make authorized API calls.
If y'all have a Google Workspace account, an administrator of the organization tin authorize an application to access user data on behalf of users in the Google Workspace domain. For example, an application that uses the Google Calendar API to add events to the calendars of all users in a Google Workspace domain would employ a service account to admission the Google Calendar API on behalf of users. Authorizing a service account to access data on behalf of users in a domain is sometimes referred to equally "delegating domain-wide authority" to a service account.
To consul domain-wide potency to a service account, a super administrator of the Google Workspace domain must complete the following steps:
- From your Google Workspace domain's Admin panel,go to Main card > Security > API Controls.
- In the Domain wide delegation pane, select Manage Domain Wide Delegation.
- Click Add together new.
- In the Customer ID field, enter the service account'south Customer ID. Y'all can find your service account'southward customer ID in the Service accounts page.
- In the OAuth scopes (comma-delimited) field, enter the list of scopes that your application should be granted access to. For case, if your application needs domain-broad total admission to the Google Drive API and the Google Agenda API, enter: https://www.googleapis.com/auth/bulldoze, https://world wide web.googleapis.com/auth/agenda.
- Click Authorize.
Your application now has the dominance to make API calls as users in your domain (to "impersonate" users). When you prepare to brand authorized API calls, you specify the user to impersonate.
Preparing to make an authorized API call
Java
Afterward you obtain the client email address and private primal from the API Console, use the Google APIs Client Library for Java to create a GoogleCredential object from the service account's credentials and the scopes your application needs admission to. For example:
import com.google.api.client.googleapis.auth.oauth2.GoogleCredential; import com.google.api.services.sqladmin.SQLAdminScopes; // ... GoogleCredential credential = GoogleCredential.fromStream(new FileInputStream("MyProject-1234.json")) .createScoped(Collections.singleton(SQLAdminScopes.SQLSERVICE_ADMIN)); If you are developing an app on Google Cloud Platform, you tin can use the application default credentials instead, which can simplify the procedure.
Delegate domain-wide authority
If you have delegated domain-wide access to the service business relationship and yous want to impersonate a user account, specify the electronic mail accost of the user account with the createDelegated method of the GoogleCredential object. For example:
GoogleCredential credential = GoogleCredential.fromStream(new FileInputStream("MyProject-1234.json")) .createScoped(Collections.singleton(SQLAdminScopes.SQLSERVICE_ADMIN)) .createDelegated("user@example.com"); Use the GoogleCredential object to phone call Google APIs in your application.
Python
Afterwards you obtain the client email address and private central from the API Console, employ the Google APIs Client Library for Python to complete the following steps:
- Create a
Credentialsobject from the service account's credentials and the scopes your application needs admission to. For example:from google.oauth2 import service_account SCOPES = ['https://world wide web.googleapis.com/auth/sqlservice.admin'] SERVICE_ACCOUNT_FILE = '/path/to/service.json' credentials = service_account.Credentials.from_service_account_file( SERVICE_ACCOUNT_FILE, scopes=SCOPES)
If you are developing an app on Google Cloud Platform, you tin use the awarding default credentials instead, which can simplify the process.
- Delegate domain-wide authority
If you have delegated domain-wide access to the service account and yous desire to impersonate a user account, use the
with_subjectmethod of an existingServiceAccountCredentialsobject. For example:delegated_credentials = credentials.with_subject('user@example.org')
Utilize the Credentials object to call Google APIs in your awarding.
HTTP/Balance
Later you obtain the client ID and private key from the API Console, your application needs to complete the following steps:
- Create a JSON Web Token (JWT, pronounced, "jot") which includes a header, a claim set up, and a signature.
- Request an access token from the Google OAuth 2.0 Authorization Server.
- Handle the JSON response that the Say-so Server returns.
The sections that follow draw how to complete these steps.
If the response includes an access token, you can use the access token to call a Google API. (If the response does not include an access token, your JWT and token asking might not be properly formed, or the service account might not take permission to admission the requested scopes.)
When the access token expires, your awarding generates another JWT, signs information technology, and requests another admission token.
The remainder of this section describes the specifics of creating a JWT, signing the JWT, forming the access token request, and handling the response.
Creating a JWT
A JWT is equanimous of iii parts: a header, a claim set, and a signature. The header and merits set are JSON objects. These JSON objects are serialized to UTF-8 bytes, then encoded using the Base64url encoding. This encoding provides resilience against encoding changes due to repeated encoding operations. The header, claim set, and signature are concatenated together with a period (.) character.
A JWT is equanimous equally follows:
{Base64url encoded header}.{Base64url encoded claim ready}.{Base64url encoded signature} The base string for the signature is as follows:
{Base64url encoded header}.{Base64url encoded claim gear up} The header consists of two fields that betoken the signing algorithm and the format of the assertion. Both fields are mandatory, and each field has only one value. As additional algorithms and formats are introduced, this header volition change accordingly.
Service accounts rely on the RSA SHA-256 algorithm and the JWT token format. As a result, the JSON representation of the header is as follows:
{"alg":"RS256","typ":"JWT"} The Base64url representation of this is as follows:
eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9
Forming the JWT claim set
The JWT claim set contains information about the JWT, including the permissions being requested (scopes), the target of the token, the issuer, the time the token was issued, and the lifetime of the token. Most of the fields are mandatory. Like the JWT header, the JWT claim set is a JSON object and is used in the calculation of the signature.
Required claims
The required claims in the JWT claim set are shown below. They may appear in any order in the claim set.
| Name | Description |
|---|---|
iss | The e-mail address of the service business relationship. |
scope | A space-delimited listing of the permissions that the awarding requests. |
aud | A descriptor of the intended target of the assertion. When making an access token request this value is always https://oauth2.googleapis.com/token. |
exp | The expiration time of the assertion, specified as seconds since 00:00:00 UTC, January 1, 1970. This value has a maximum of ane hour after the issued time. |
iat | The time the exclamation was issued, specified as seconds since 00:00:00 UTC, January one, 1970. |
The JSON representation of the required fields in a JWT claim set is shown below:
{ "iss": "761326798069-r5mljlln1rd4lrbhg75efgigp36m78j5@developer.gserviceaccount.com", "scope": "https://world wide web.googleapis.com/auth/devstorage.read_only", "aud": "https://oauth2.googleapis.com/token", "exp": 1328554385, "iat": 1328550785 } Additional claims
In some enterprise cases, an application can use domain-broad delegation to act on behalf of a particular user in an system. Permission to perform this type of impersonation must exist granted before an awarding tin impersonate a user, and is commonly handled by a super administrator. For more information, see Control API access with domain-broad delegation.
To obtain an access token that grants an awarding delegated admission to a resources, include the email address of the user in the JWT claim fix every bit the value of the sub field.
| Name | Description |
|---|---|
sub | The email address of the user for which the application is requesting delegated access. |
If an application does non take permission to impersonate a user, the response to an access token asking that includes the sub field volition be an error.
An example of a JWT claim gear up that includes the sub field is shown below:
{ "iss": "761326798069-r5mljlln1rd4lrbhg75efgigp36m78j5@developer.gserviceaccount.com", "sub": "some.user@instance.com", "scope": "https://world wide web.googleapis.com/auth/prediction", "aud": "https://oauth2.googleapis.com/token", "exp": 1328554385, "iat": 1328550785 } Encoding the JWT claim set
Like the JWT header, the JWT claim set should exist serialized to UTF-eight and Base64url-safety encoded. Below is an example of a JSON representation of a JWT Claim gear up:
{ "iss": "761326798069-r5mljlln1rd4lrbhg75efgigp36m78j5@developer.gserviceaccount.com", "scope": "https://world wide web.googleapis.com/auth/prediction", "aud": "https://oauth2.googleapis.com/token", "exp": 1328554385, "iat": 1328550785 } Calculating the signature
JSON Web Signature (JWS) is the specification that guides the mechanics of generating the signature for the JWT. The input for the signature is the byte array of the following content:
{Base64url encoded header}.{Base64url encoded merits set up} The signing algorithm in the JWT header must be used when computing the signature. The merely signing algorithm supported by the Google OAuth 2.0 Say-so Server is RSA using SHA-256 hashing algorithm. This is expressed every bit RS256 in the alg field in the JWT header.
Sign the UTF-8 representation of the input using SHA256withRSA (also known as RSASSA-PKCS1-V1_5-SIGN with the SHA-256 hash office) with the private key obtained from the Google API Console. The output volition be a byte array.
The signature must then exist Base64url encoded. The header, merits set, and signature are concatenated together with a period (.) character. The result is the JWT. Information technology should exist the post-obit (line breaks added for clarity):
{Base64url encoded header}. {Base64url encoded claim set}. {Base64url encoded signature} Below is an case of a JWT earlier Base64url encoding:
{"alg":"RS256","typ":"JWT"}. { "iss":"761326798069-r5mljlln1rd4lrbhg75efgigp36m78j5@programmer.gserviceaccount.com", "scope":"https://www.googleapis.com/auth/prediction", "aud":"https://oauth2.googleapis.com/token", "exp":1328554385, "iat":1328550785 }. [signature bytes] Below is an example of a JWT that has been signed and is prepare for transmission:
eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiI3NjEzMjY3OTgwNjktcjVtbGpsbG4xcmQ0bHJiaGc3NWVmZ2lncDM2bTc4ajVAZGV2ZWxvcGVyLmdzZXJ2aWNlYWNjb3VudC5jb20iLCJzY29wZSI6Imh0dHBzOi8vd3d3Lmdvb2dsZWFwaXMuY29tL2F1dGgvcHJlZGljdGlvbiIsImF1ZCI6Imh0dHBzOi8vd3d3Lmdvb2dsZWFwaXMuY29tL29hdXRoMi92NC90b2tlbiIsImV4cCI6MTMyODU1NDM4NSwiaWF0IjoxMzI4NTUwNzg1fQ.UFUt59SUM2_AW4cRU8Y0BYVQsNTo4n7AFsNrqOpYiICDu37vVt-tw38UKzjmUKtcRsLLjrR3gFW3dNDMx_pL9DVjgVHDdYirtrCekUHOYoa1CMR66nxep5q5cBQ4y4u2kIgSvChCTc9pmLLNoIem-ruCecAJYgI9Ks7pTnW1gkOKs0x3YpiLpzplVHAkkHztaXiJdtpBcY1OXyo6jTQCa3Lk2Q3va1dPkh_d--GU2M5flgd8xNBPYw4vxyt0mP59XZlHMpztZt0soSgObf7G3GXArreF_6tpbFsS3z2t5zkEiHuWJXpzcYr5zWTRPDEHsejeBSG8EgpLDce2380ROQ
Making the access token request
Afterward generating the signed JWT, an application can use information technology to request an access token. This access token request is an HTTPS Mail request, and the trunk is URL encoded. The URL is shown below:
https://oauth2.googleapis.com/token
The following parameters are required in the HTTPS POST request:
| Name | Clarification |
|---|---|
grant_type | Use the following string, URL-encoded as necessary: urn:ietf:params:oauth:grant-type:jwt-bearer |
assertion | The JWT, including signature. |
Below is a raw dump of the HTTPS Mail service asking used in an access token request:
Postal service /token HTTP/one.1 Host: oauth2.googleapis.com Content-Type: application/x-www-grade-urlencoded grant_type=urn%3Aietf%3Aparams%3Aoauth%3Agrant-type%3Ajwt-bearer&assertion=eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiI3NjEzMjY3OTgwNjktcjVtbGpsbG4xcmQ0bHJiaGc3NWVmZ2lncDM2bTc4ajVAZGV2ZWxvcGVyLmdzZXJ2aWNlYWNjb3VudC5jb20iLCJzY29wZSI6Imh0dHBzOi8vd3d3Lmdvb2dsZWFwaXMuY29tL2F1dGgvcHJlZGljdGlvbiIsImF1ZCI6Imh0dHBzOi8vYWNjb3VudHMuZ29vZ2xlLmNvbS9vL29hdXRoMi90b2tlbiIsImV4cCI6MTMyODU3MzM4MSwiaWF0IjoxMzI4NTY5NzgxfQ.ixOUGehweEVX_UKXv5BbbwVEdcz6AYS-6uQV6fGorGKrHf3LIJnyREw9evE-gs2bmMaQI5_UbabvI4k-mQE4kBqtmSpTzxYBL1TCd7Kv5nTZoUC1CmwmWCFqT9RE6D7XSgPUh_jF1qskLa2w0rxMSjwruNKbysgRNctZPln7cqQ
Below is the same request, using gyre:
curlicue -d 'grant_type=urn%3Aietf%3Aparams%3Aoauth%3Agrant-type%3Ajwt-bearer&exclamation=eyJhbGciOiJSUzI1NiIsInR5cCI6IkpXVCJ9.eyJpc3MiOiI3NjEzMjY3OTgwNjktcjVtbGpsbG4xcmQ0bHJiaGc3NWVmZ2lncDM2bTc4ajVAZGV2ZWxvcGVyLmdzZXJ2aWNlYWNjb3VudC5jb20iLCJzY29wZSI6Imh0dHBzOi8vd3d3Lmdvb2dsZWFwaXMuY29tL2F1dGgvcHJlZGljdGlvbiIsImF1ZCI6Imh0dHBzOi8vYWNjb3VudHMuZ29vZ2xlLmNvbS9vL29hdXRoMi90b2tlbiIsImV4cCI6MTMyODU3MzM4MSwiaWF0IjoxMzI4NTY5NzgxfQ.RZVpzWygMLuL-n3GwjW1_yhQhrqDacyvaXkuf8HcJl8EtXYjGjMaW5oiM5cgAaIorrqgYlp4DPF_GuncFqg9uDZrx7pMmCZ_yHfxhSCXru3gbXrZvAIicNQZMFxrEEn4REVuq7DjkTMyCMGCY1dpMa8aWfTQFt3Eh7smLchaZsU ' https://oauth2.googleapis.com/token
Treatment the response
If the JWT and access token request are properly formed and the service account has permission to perform the performance, then the JSON response from the Authorisation Server includes an access token. The post-obit is an example response:
{ "access_token": "1/8xbJqaOZXSUZbHLl5EOtu1pxz3fmmetKx9W8CV4t79M", "scope": "https://world wide web.googleapis.com/auth/prediction" "token_type": "Bearer", "expires_in": 3600 } Access tokens can be reused during the duration window specified by the expires_in value.
Calling Google APIs
Coffee
Utilize the GoogleCredential object to telephone call Google APIs by completing the following steps:
- Create a service object for the API that you want to telephone call using the
GoogleCredentialobject. For example:SQLAdmin sqladmin = new SQLAdmin.Architect(httpTransport, JSON_FACTORY, credential).build();
- Make requests to the API service using the interface provided past the service object. For example, to list the instances of Cloud SQL databases in the exciting-example-123 project:
SQLAdmin.Instances.List instances = sqladmin.instances().list("exciting-case-123").execute();
Python
Use the authorized Credentials object to phone call Google APIs by completing the post-obit steps:
- Build a service object for the API that you lot want to telephone call. You build a a service object by calling the
buildfunction with the name and version of the API and the authorizedCredentialsobject. For example, to telephone call version 1beta3 of the Cloud SQL Administration API:import googleapiclient.discovery sqladmin = googleapiclient.discovery.build('sqladmin', 'v1beta3', credentials=credentials) - Make requests to the API service using the interface provided by the service object. For example, to listing the instances of Cloud SQL databases in the exciting-instance-123 project:
response = sqladmin.instances().listing(project='exciting-example-123').execute()
HTTP/REST
Later on your application obtains an access token, y'all can employ the token to make calls to a Google API on behalf of a given service business relationship or user business relationship if the scope(s) of access required past the API have been granted. To practice this, include the access token in a asking to the API by including either an access_token query parameter or an Authorization HTTP header Bearer value. When possible, the HTTP header is preferable, because query strings tend to exist visible in server logs. In most cases you can use a customer library to fix upward your calls to Google APIs (for instance, when calling the Bulldoze Files API).
You tin can endeavour out all the Google APIs and view their scopes at the OAuth 2.0 Playground.
HTTP GET examples
A call to the drive.files endpoint (the Drive Files API) using the Authorization: Bearer HTTP header might wait similar the post-obit. Note that you need to specify your ain access token:
Become /drive/v2/files HTTP/i.i Host: world wide web.googleapis.com Authorisation: Bearer access_token
Here is a telephone call to the same API for the authenticated user using the access_token query cord parameter:
GET https://www.googleapis.com/drive/v2/files?access_token=access_token
whorl examples
You can exam these commands with the curl command-line awarding. Hither's an example that uses the HTTP header selection (preferred):
curl -H "Authorization: Bearer access_token" https://www.googleapis.com/drive/v2/files
Or, alternatively, the query string parameter pick:
curl https://www.googleapis.com/drive/v2/files?access_token=access_token
When access tokens elapse
Access tokens issued by the Google OAuth two.0 Authorization Server elapse after the duration provided past the expires_in value. When an access token expires, then the application should generate another JWT, sign it, and request some other admission token.
JWT mistake codes
fault field | error_description field | Meaning | How to resolve |
|---|---|---|---|
unauthorized_client | Unauthorized customer or scope in asking. | If yous're trying to utilize domain-wide delegation, the service account is non authorized in the Admin console of the user's domain. | Ensure that the service account is authorized in the Domain-wide delegation folio of the Admin console for the user in the While it normally takes a few minutes, it might take up to 24 hours for authorization to propagate to all users in your Google Account. |
unauthorized_client | Customer is unauthorized to retrieve access tokens using this method, or client not authorized for whatsoever of the scopes requested. | A service business relationship was authorized using the client email address rather than the client ID (numeric) in the Admin console. | In the Domain-wide delegation page in the Admin console, remove the client, and re-add together it with the numeric ID. |
access_denied | (any value) | If you're using Domain-broad delegation, 1 or more requested scopes aren't authorized in the Admin console. | Ensure that the service business relationship is authorized in the Domain-broad delegation page of the Admin console for the user in the While it unremarkably takes a few minutes, it might take upward to 24 hours for dominance to propagate to all users in your Google Account. |
invalid_grant | Non a valid email. | The user doesn't be. | Check that the e-mail address in the sub claim (field) is correct. |
invalid_grant | | Normally, information technology means that the local system time is not correct. Information technology could also happen if the exp value is more than 65 mins in the future from the iat value, or the exp value is lower than iat value. | Brand certain that the clock on the organisation where the JWT is generated is correct. If necessary, sync your time with Google NTP. |
invalid_grant | Invalid JWT Signature. | The JWT assertion is signed with a private key not associated with the service account identified by the client electronic mail or the central that was used has been deleted, disabled, or has expired. Alternatively, the JWT exclamation might be encoded incorrectly - information technology must exist Base64-encoded, without newlines or padding equal signs. | Decode the JWT merits set and verify the key that signed the assertion is associated with the service account. Try to use a Google-provided OAuth library to make sure the JWT is generated correctly. |
invalid_scope | Invalid OAuth scope or ID token audience provided. | No scopes were requested (empty list of scopes), or ane of the requested scopes doesn't be (i.e. is invalid). | Ensure that the Note that the list of scopes in the |
disabled_client | The OAuth client was disabled. | The key used to sign the JWT assertion is disabled. | Go to the Google API Console, and under IAM & Admin > Service Accounts, enable the service account which contains the "Key ID" used to sign the assertion. |
Addendum: Service account authorization without OAuth
With some Google APIs, you can make authorized API calls using a signed JWT straight as a bearer token, rather than an OAuth 2.0 access token. When this is possible, you can avoid having to brand a network request to Google's authorization server earlier making an API call.
If the API you want to call has a service definition published in the Google APIs GitHub repository, you can make authorized API calls using a JWT instead of an access token. To practise and so:
- Create a service account as described above. Be certain to go along the JSON file yous get when y'all create the business relationship.
- Using any standard JWT library, such as one plant at jwt.io, create a JWT with a header and payload similar the post-obit example:
{ "alg": "RS256", "typ": "JWT", "kid": "abcdef1234567890" } . { "iss": "123456-compute@developer.gserviceaccount.com", "sub": "123456-compute@developer.gserviceaccount.com", "aud": "https://firestore.googleapis.com/", "iat": 1511900000, "exp": 1511903600 } - For the
kidfield in the header, specify your service account's private fundamental ID. You can detect this value in theprivate_key_idfield of your service account JSON file. - For the
issandsubfields, specify your service account's email address. You lot can observe this value in theclient_emailfield of your service business relationship JSON file. - For the
audfield, specify the API endpoint. For example:https://SERVICE.googleapis.com/. - For the
iatfield, specify the current Unix time, and for theexpfield, specify the time exactly 3600 seconds later, when the JWT will expire.
Sign the JWT with RSA-256 using the individual key found in your service account JSON file.
For example:
Java
Using google-api-java-client and java-jwt:
GoogleCredential credential = GoogleCredential.fromStream(new FileInputStream("MyProject-1234.json")); PrivateKey privateKey = credential.getServiceAccountPrivateKey(); String privateKeyId = credential.getServiceAccountPrivateKeyId(); long now = Organization.currentTimeMillis(); try { Algorithm algorithm = Algorithm.RSA256(nothing, privateKey); String signedJwt = JWT.create() .withKeyId(privateKeyId) .withIssuer("123456-compute@developer.gserviceaccount.com") .withSubject("123456-compute@programmer.gserviceaccount.com") .withAudience("https://firestore.googleapis.com/") .withIssuedAt(new Date(at present)) .withExpiresAt(new Appointment(now + 3600 * 1000L)) .sign(algorithm); } catch ... Python
Using PyJWT:
iat = time.fourth dimension() exp = iat + 3600 payload = {'iss': '123456-compute@programmer.gserviceaccount.com', 'sub': '123456-compute@developer.gserviceaccount.com', 'aud': 'https://firestore.googleapis.com/', 'iat': iat, 'exp': exp} additional_headers = {'child': PRIVATE_KEY_ID_FROM_JSON} signed_jwt = jwt.encode(payload, PRIVATE_KEY_FROM_JSON, headers=additional_headers, algorithm='RS256') - Call the API, using the signed JWT as the bearer token:
GET /v1/projects/abc/databases/123/indexes HTTP/1.1 Authorization: Bearer SIGNED_JWT Host: firestore.googleapis.com
Source: https://developers.google.com/identity/protocols/oauth2/service-account
0 Response to "Java Google Http Client Application/x-www-form-urlencoded File Upload"
Post a Comment